What is UpGuard Breach Risk?
UpGuard Breach Risk identifies the cyber-related risks that your company is directly exposed to.
The Breach Risk module of the UpGuard platform is where you can monitor and manage cyber-related risks that your company is directly exposed to. These include:
- Risk Profile: Risks identified in the configuration of your Internet presence are broken down into categories.
- Identity Breaches: Third-party data breaches that include credentials (email addresses) belonging to your company.
- Data Leaks: Data belonging to your company that is exposed on the Internet.
Risk Profile
The Risk Profile section shows the list of active risks that are associated with your company's domains.

To get more information on a particular risk, simply click on the row in the table and a panel will open on the right side of your screen. In this panel, you can find the risk summary, affected assets, and recommended remediation steps.
Identity Breaches
The Identity Breaches section shows where your company email addresses have been exposed in third-party data breaches. You’ll see the name of the breach, the date it occurred, and how many emails (associated with your company) were included in the breach.
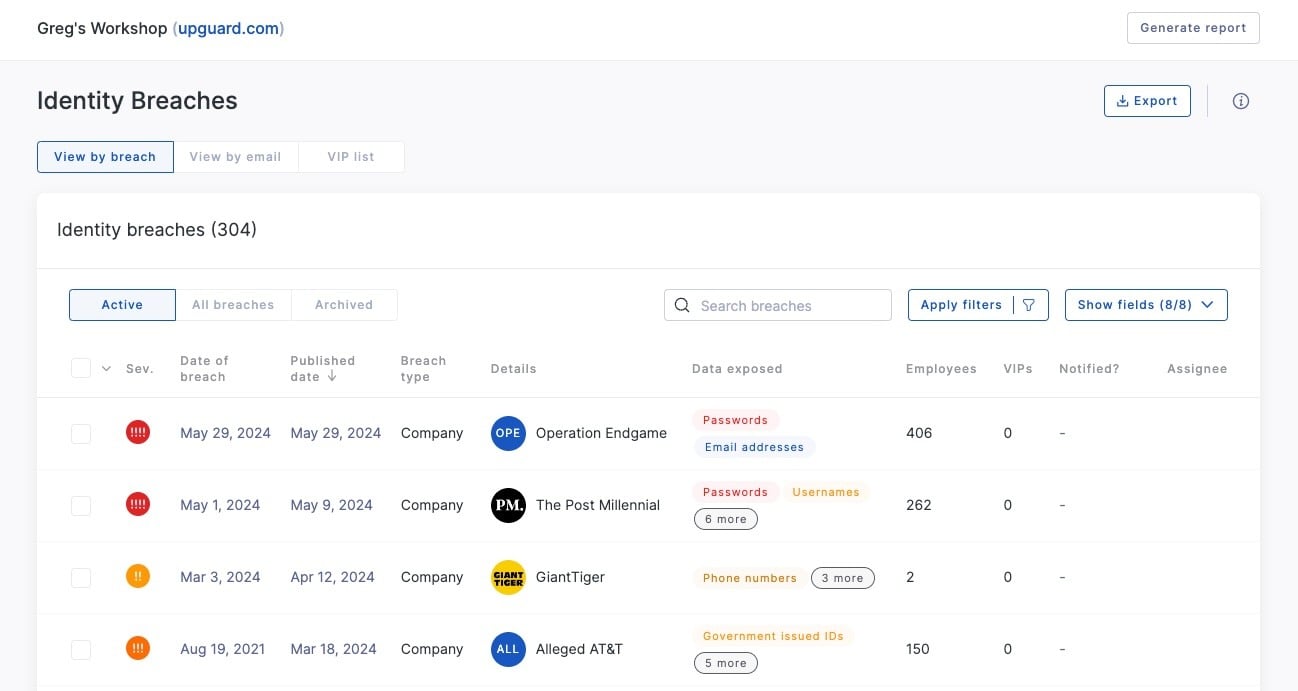
To learn more about a breach, simply click on the one you’re curious about. At the top of the page, you’ll see a summary of where the breach originated, how many people were impacted, and any other relevant data. Below that, you’ll see a list of all the emails in your organization that were part of the breach in question.
Findings are automatically sorted by date, with most recent showing up at the top. You can also sort by name or number of employees involved by clicking on the relevant header
Typosquatting
The Typosquatting module helps you monitor cybersecurity risks related to typosquatting. It lets you choose the domains you want to monitor and identifies permutations of those domains that are at risk of typosquatting.
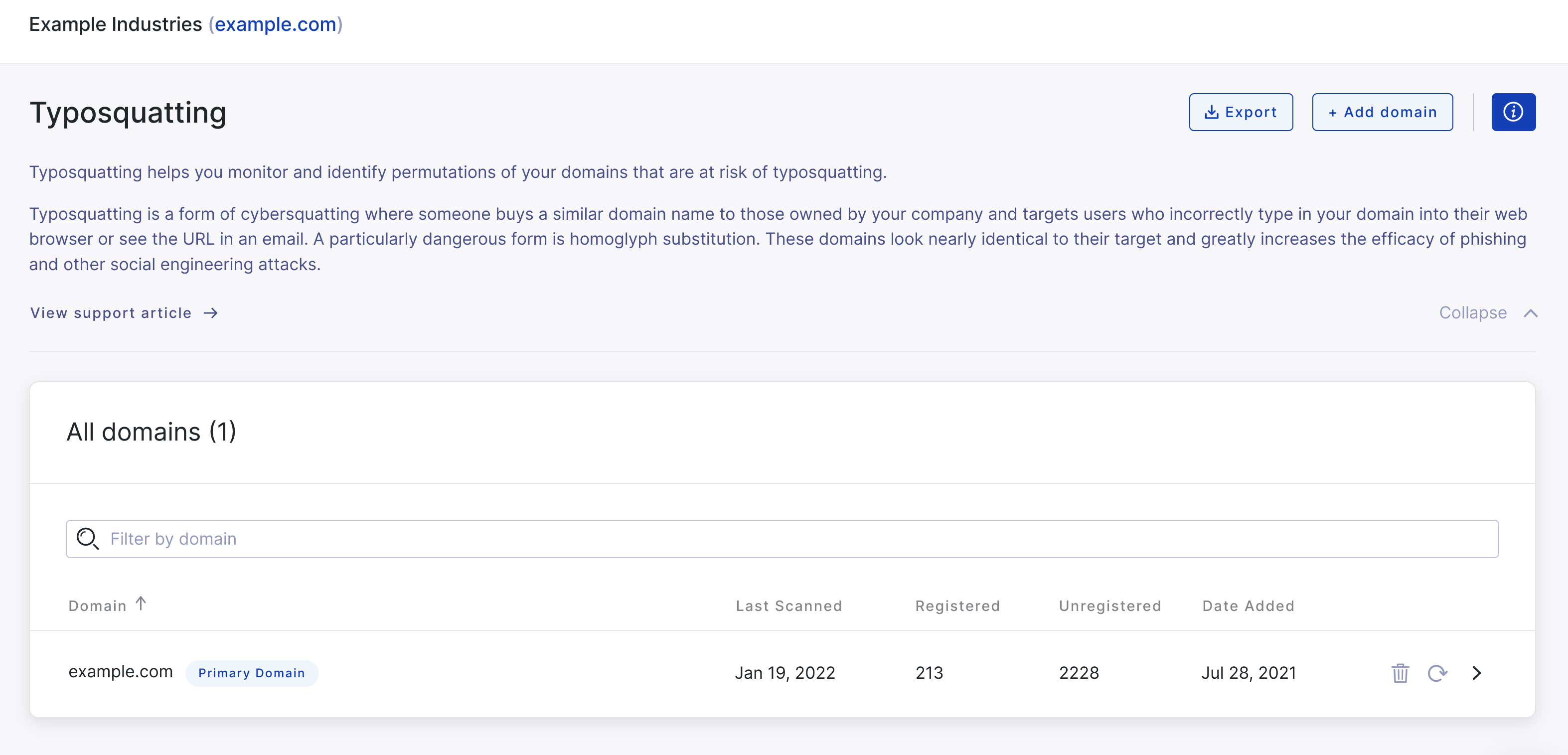
Learn more about typosquatting here.
See also:
