How to generate a Vendor risk report
Learn how to generate a vendor report that can be shared with colleagues, board members, or employees of a vendor.
Our Vendor Report feature generates a downloadable PDF or Word document that summarizes the security posture of any of your monitored vendors. The report is designed to be shared with internal and external stakeholders who are not UpGuard users, such as a colleague, board member or employees of the associated vendor.
The language is simple, easy-to-understand, and suitable for non-technical audiences.
When shared with colleagues, reports can be used to drive decision-making, speed up vendor due diligence, and highlight high-risk vendors that should no longer be used.
When shared with vendors, the report can aid in remediation efforts. Giving vendors access to their risk profile creates open, effective dialogue and empowers them to take action to remediate risks. This directly translates to a reduced risk for your organization.
To aid in remediation efforts, the report unpacks the vendor's security posture into six underlying categories: questionnaire, website security, network security, brand & reputation risk, email security, and phishing & malware.
Each category outlines individual risks, domains impacted, and provides remediation advice. The most severe risks in each category appear first.
Configuration options
What makes these reports so effective is UpGuard’s ability to combine real-time threat signals with traditional risk management techniques. This combination provides a complete picture of the vendor’s cybersecurity risk.
These configuration options provide flexibility, while ensuring that the report can provide a complete overview of your vendor’s risk profile.
Generating a report
Before you can run a report, you need to be monitoring the vendor. If you aren't currently monitoring the vendor, you can learn how to monitor them here.
You can generate a report for a monitored vendor in 2 ways:
1. Generating a Vendor Report from the Reports Library
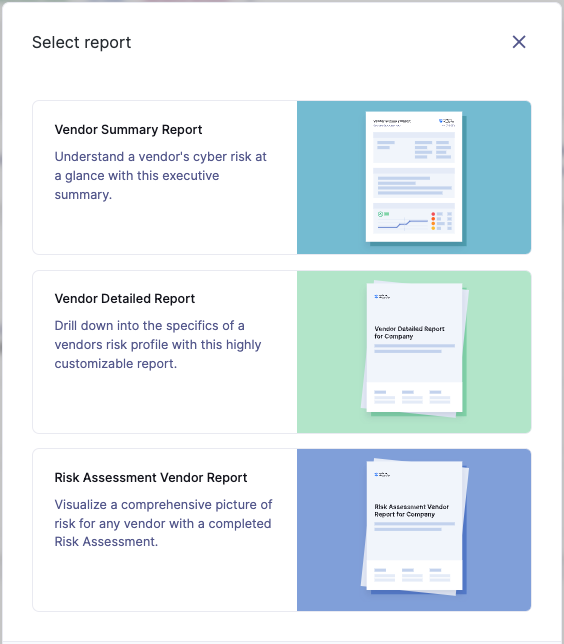
Navigate to Reports > Templates and select from the available vendor reports: Vendor Summary Report, Vendor Detailed Report, Security Profile Risk Assessment Report and the Vendor Risk Assessment Report.

For each report you can choose Quick generate which pre-selects the default report content and sections, or Customize and generate if you want to customize and curate your report content.
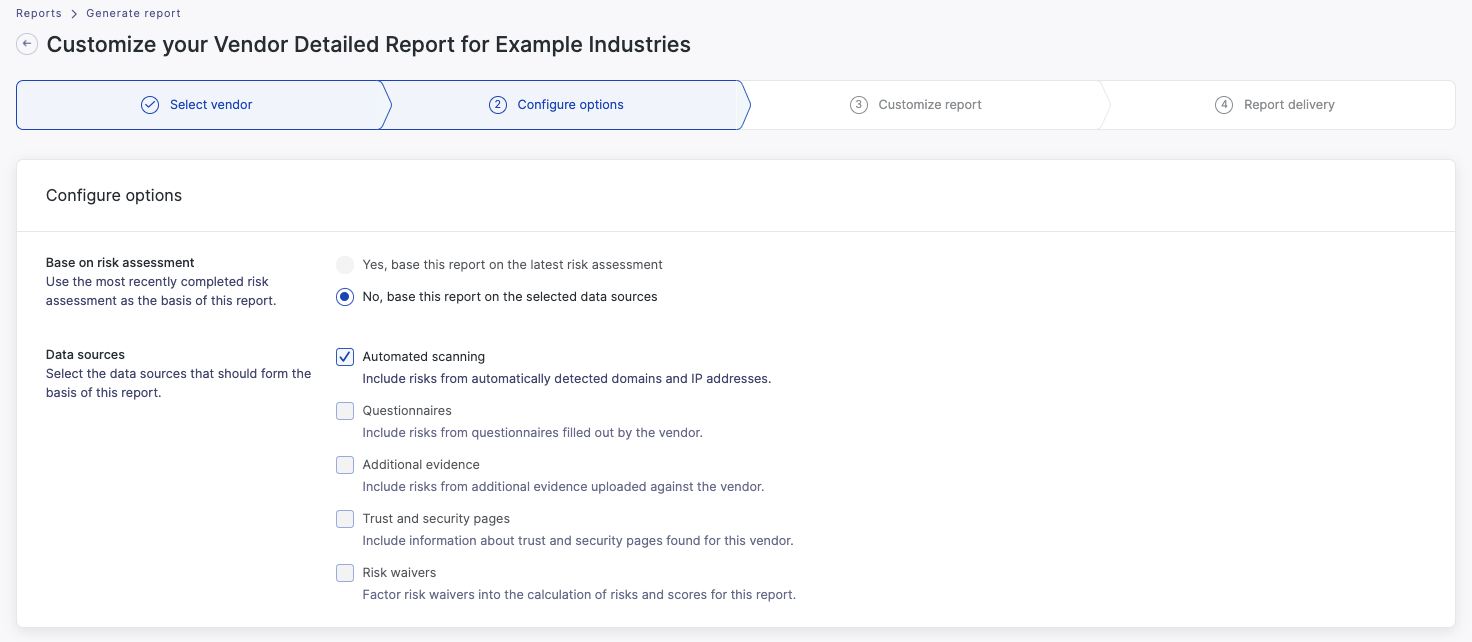
If you select Customize and generate, firstly you will be asked to select the vendor you want to run the report for, and then you will be able to choose which data you want to base your report on. Reports can be based on a risk assessment conducted on the UpGuard platform or a combination of automated scanning results, security questionnaires, additional evidence and other risk management activities conducted in the platform. If a report is based on a risk assessment, automated scanning results (and any other information) will be based on the data sources you included in your risk assessment, and the data available at the time of the assessment. Otherwise, results are based on the latest available information.
Once you have selected your data sources, you will be able to select what type of information you want to include in your report, based on risk profile information in the UpGuard platform. You can also reorder the report sections according to your specific requirements.
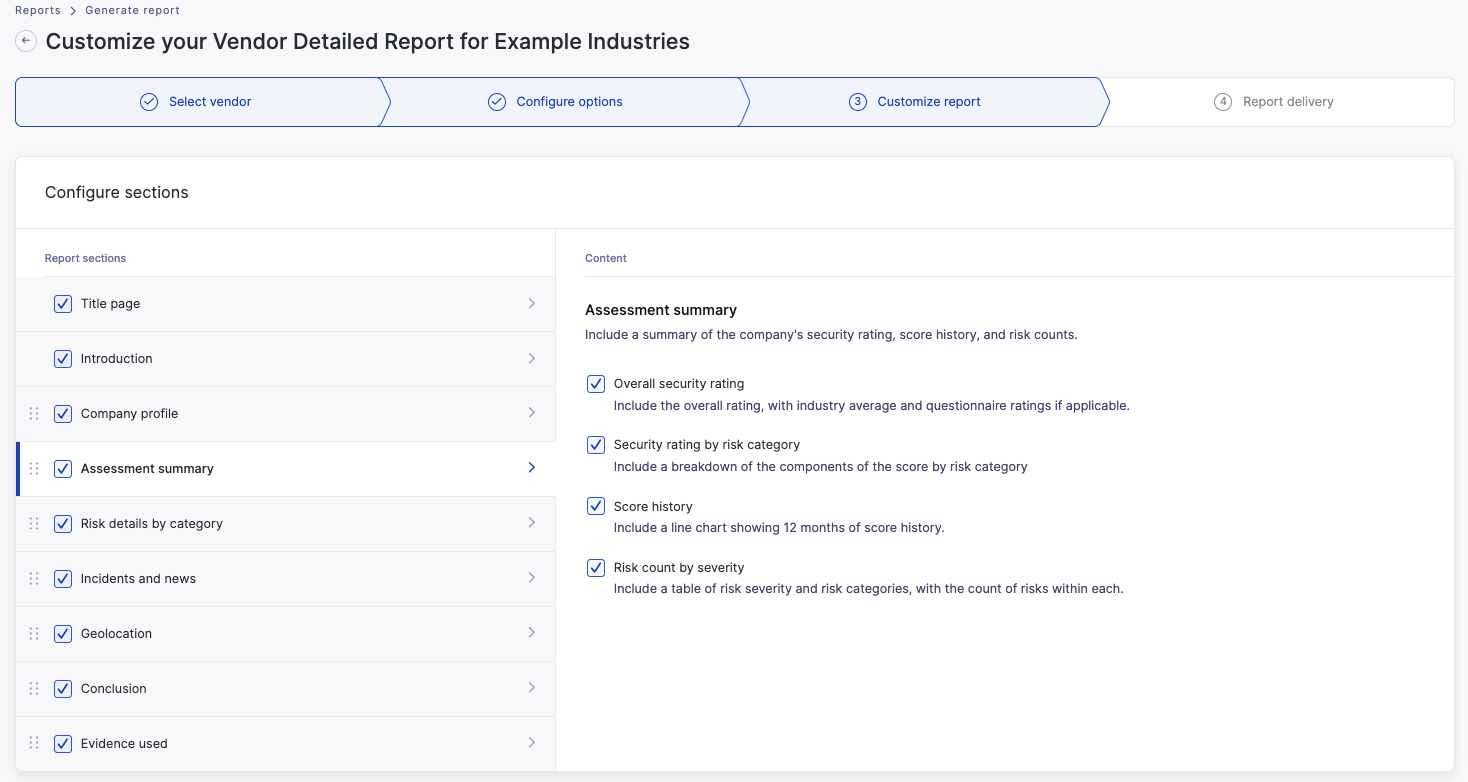
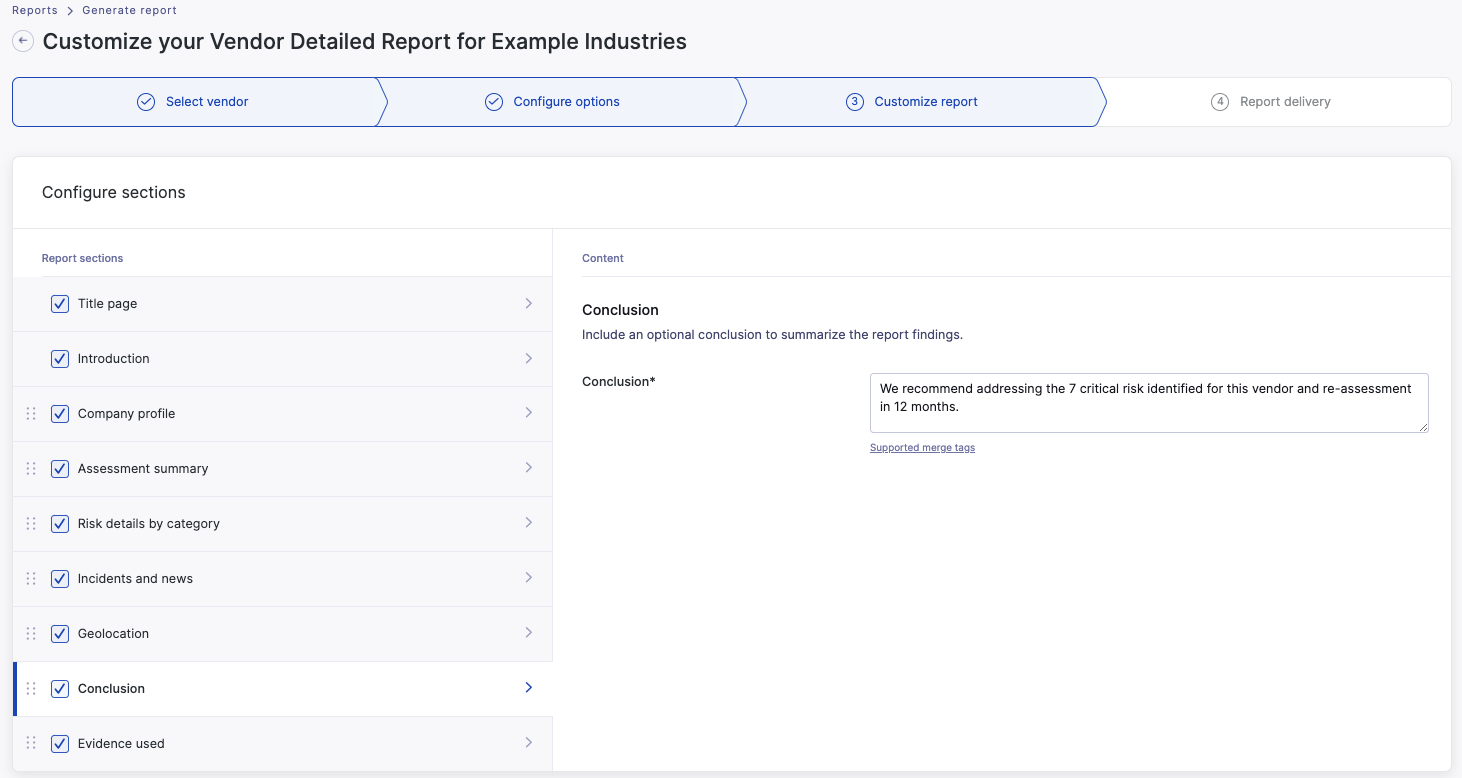
You can also edit the report introduction and add a custom conclusion to capture your recommendations.
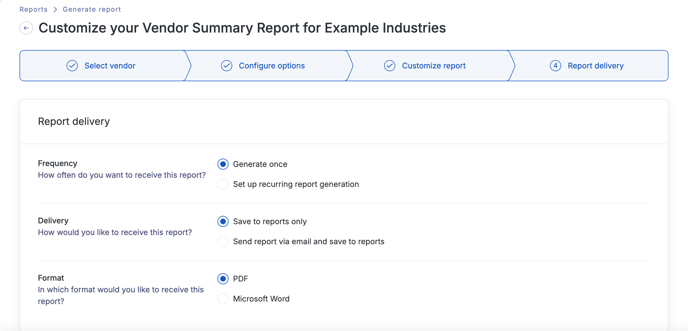
You can then select from standard frequency and delivery options for the report, and whether this report should be a PDF or Word document, and then generate the report.
You can also create a custom vendor report template that can be used by you and others in your organization if you have a set report format that you want to reuse repeatedly over time. To learn more see how to create a custom report template.

2. Generating a vendor report when viewing a vendor in Vendor Risk
Select the Generate report button when you are viewing any page for an individual vendor within Vendor Risk.

You will then be able to select the report type, and follow the customization and report configuration prompts as per generating the report from the report page (described above).
How to download your vendor reports
Like all reports and exports in the UpGuard platform, your report will be made available for download via our Generated reports page.

Understanding the Vendor report options
There are 3 vendor reports with varying information and level of detail, designed to suit different functions and suitable for different stakeholders:
-
Vendor Summary Report
-
Vendor Detailed Report
-
Vendor Risk Assessment Report
The Vendor Summary Report provides a high-level overview of a vendor's security posture including category score breakdowns and overall risk counts.

The Vendor Detailed Report includes more detail including list of risks and remediation recommendations and historical risk rating by category.

The Vendor Risk Assessment Report presents the results of a point-in-time risk assessment conducted on the UpGuard platform based on the data sources and risk assessment commentary included in that risk assessment.
Keep in mind that by selecting customize and generate, you are able to curate the reporting content in any of these reports to meet your specific needs, as described earlier in this article.
See also:
