How to investigate and verify a risk finding?
Learn how to verify and investigate risk findings in UpGuard
If you suspect you have found a risk that you do not believe is correct, or your organization feels the particular risk does not apply to your organization, we recommend you make the following checks.
UpGuard collects data to assess the security posture of millions of organizations every day. We use threat signals gathered from trusted commercial, open-source, and proprietary sources, alongside risks identified in security questionnaires and risk assessments conducted on the UpGuard platform.
These threat signals are open and accessible from the public Internet, which means we only use non-intrusive techniques to gather information. We will never attempt to bypass any security controls an organization has in place.
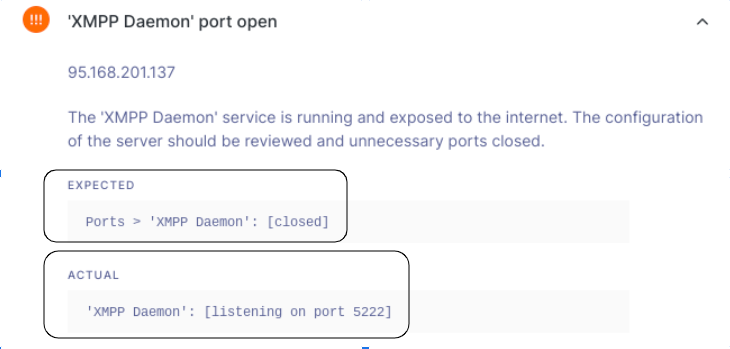
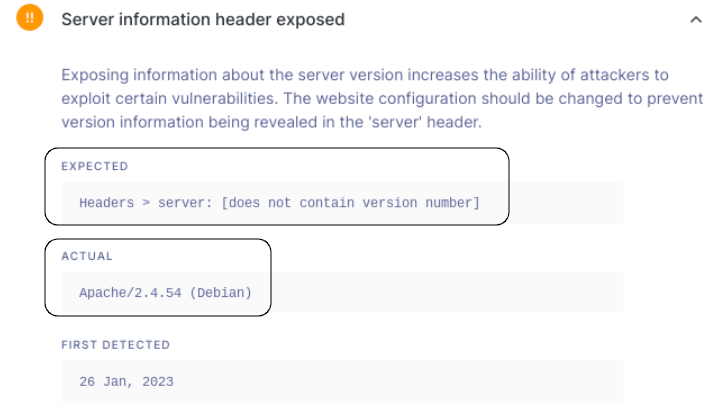
UpGuard's scanners auto-detect risks on your public facing assets, and the detected risks are listed in your Risk Profile. To view the details of a risk, you can click on it and see the details of that risk, the 'expected finding' and the 'actual finding' for the risk.
To understand the details of the risk within your own organization's environment, review your domain or IP setup to verify if the settings are as per the 'expected value' listed against the risk.
From here, you can choose to create a Risk Waiver for the risk or remediate the risk to remove the risk from your organization's attack surface.
If you have compensating controls in place that you deem to be sufficient, the recommended action would be to apply a Risk Waiver or a Public Risk Waiver and add a summary about why this risk is not applicable to your organization.
If you still have questions about a detected risk, believe the finding is a "False-positive", or is otherwise inaccurate, our Support Team is equipped to investigate and replicate findings, and work with you on identifying and remediating these risks where applicable.
