What is Exploit Prediction Scoring System (EPSS)?
UpGuard incorporates FIRST's Exploit Prediction Scoring System (EPSS) to help prioritize vulnerabilities most likely to be exploited.
The Exploit Prediction Scoring System (EPSS) helps to answer the question "which vulnerabilities should I fix?" by looking for features of vulnerabilities that are commonly exploited compared to those that aren't. Since only a small fraction of vulnerabilities are exploited at a given time, and remediating vulnerabilities requires some resource allocation, remediation efforts must be prioritized. EPSS uses historical data to identify the features that can predict whether new vulnerabilities are likely to be exploited to improve those prioritization decisions.
In UpGuard, you can use EPSS to help prioritize vulnerabilities in conjunction with other data points like CVSS and inclusion in the Known Exploited Vulnerabilities catalog.
The EPSS model calculates scores for each CVE daily representing the probability that a CVE will be exploited in the next 30 days. These scores are probabilistic; a high EPSS is not a guarantee of exploitation, nor is a low EPSS a guarantee that a vulnerability won't be exploited.
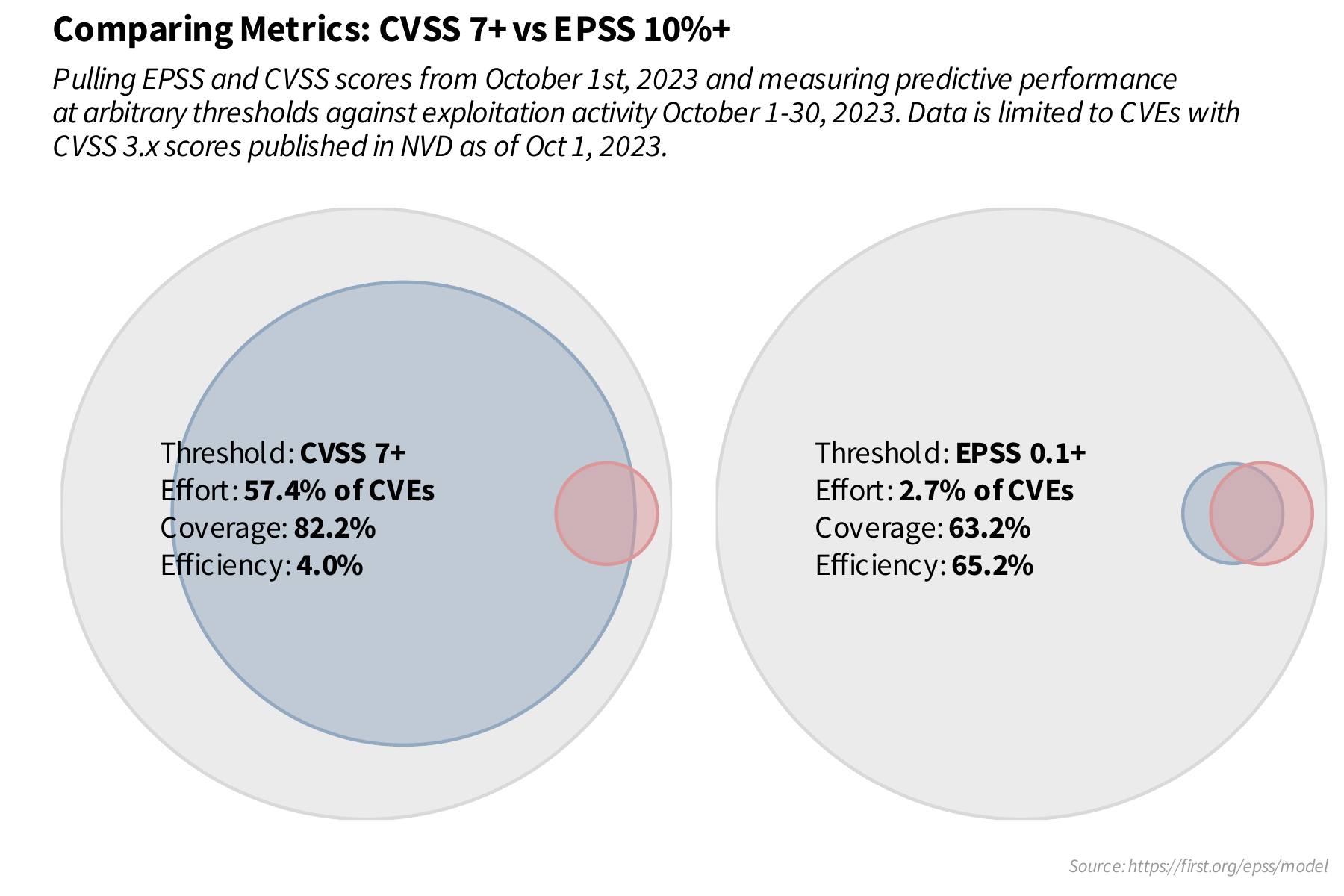
This diagram from FIRST demonstrates the benefit of EPSS compared to CVSS for avoiding wasted effort. Remediating all CVEs with CVSS >=7 fixes 82% of exploited vulnerabilities, but at the cost of also fixing many vulnerabilities that wouldn't have been exploited anyways– 96% of the effort is waste. Remediating all CVEs with EPSS >= 10% fixes 63% of exploited vulnerabilities but with much less effort spent on vulnerabilities that wouldn't have been exploited.
Balancing coverage and efficiency
In both cases, the example thresholds are chosen arbitrarily and should be based on an organization's risk tolerance. One could certainly choose an EPSS threshold that covers 80% of exploited vulnerabilities, or a lower CVSS threshold that covers less. FIRST provides a chart measuring the cost to achieve different levels of coverage with the two models:
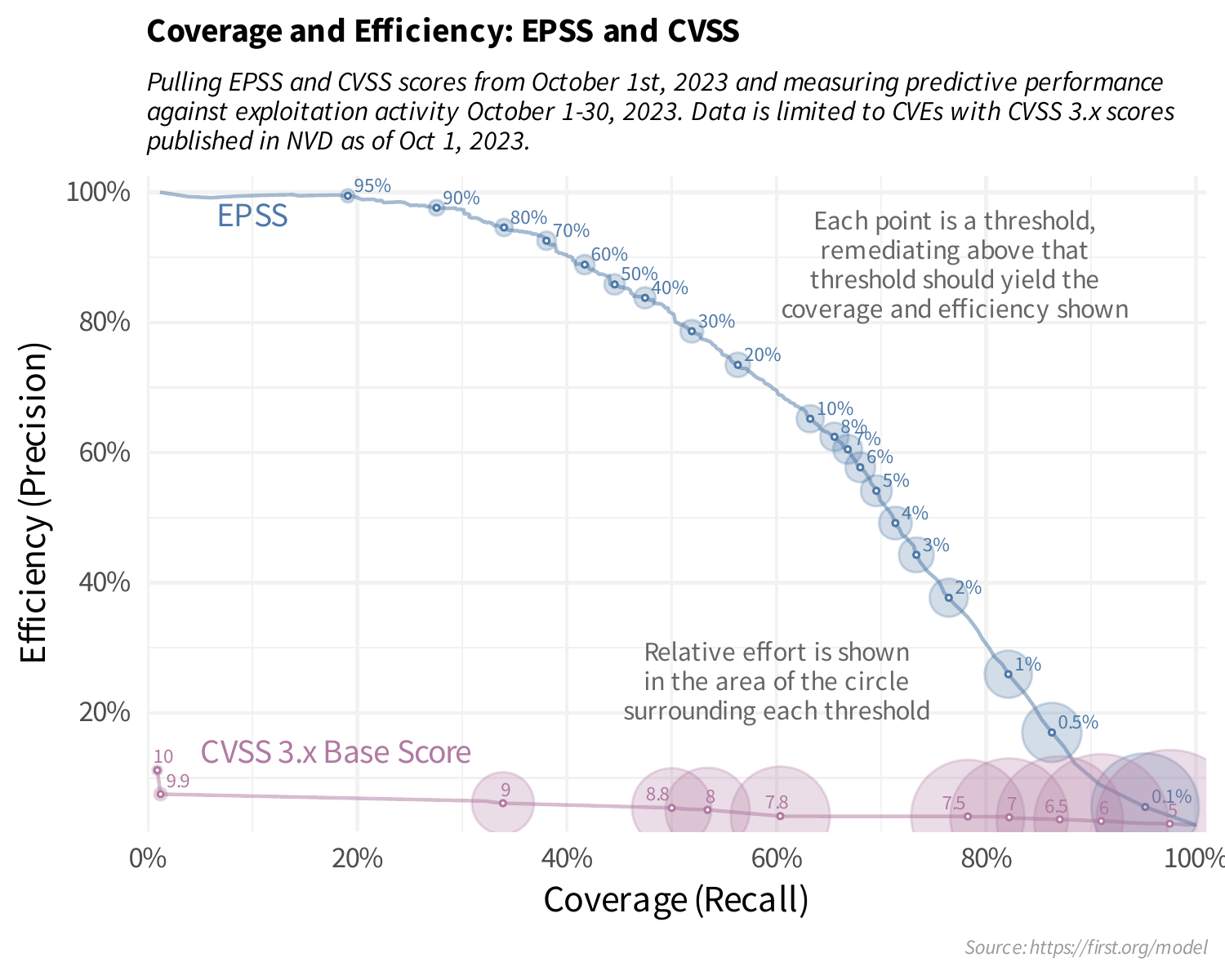
If we remediate all CVEs with a CVSS of >=9 we get comparable coverage to remediating all vulnerabilities with an EPSS of >=80%, but we would have to remediate ten times as many vulnerabilities if we select the vulnerabilities using CVSS.
For more information, you can see the EPSS site and in particular the detailed explanation of the model and how it compares to CVSS.
Using EPSS in UpGuard
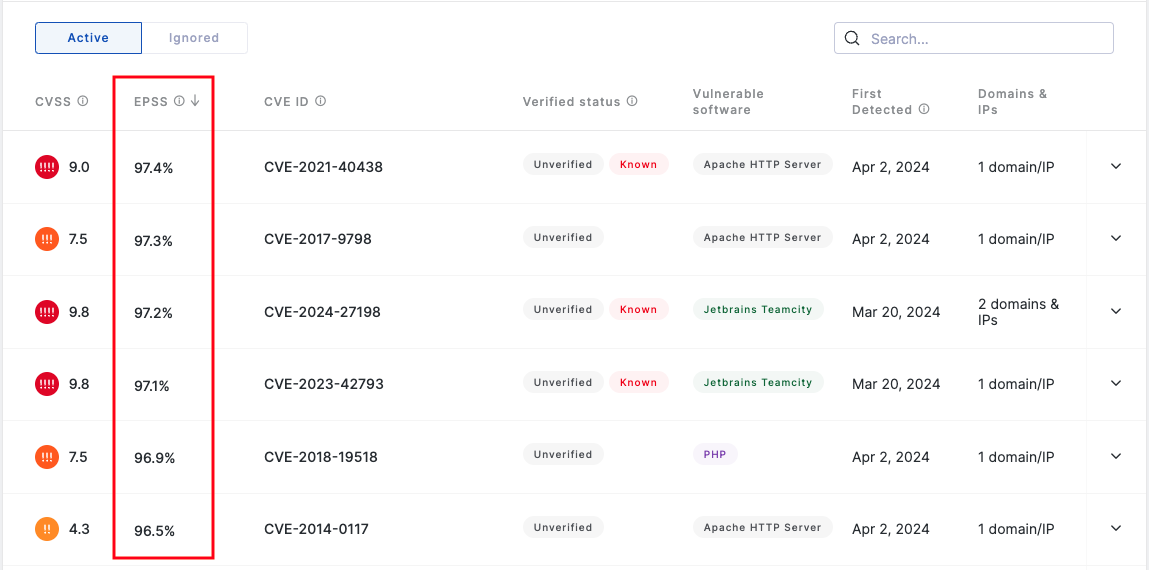
The Vulnerabilities page includes a column for EPSS, presented as the percentage likelihood of each CVE being exploited in the next 30 days. Sorting the Vulnerabilities page by EPSS can highlight a short list of vulnerabilities most at risk. Using other data points, like whether the vulnerability has been verified, it's CVSS, and whether it is known to be exploited, you can prioritize which vulnerabilities to investigate.
Not surprisingly, there tends to be quite a bit of overlap between high CVSS, high EPSS, and known exploitation– strong signals that these vulnerabilities should be treated. However, there are also instances where these methods differ, providing better insight into the exploitability of your attack surface.
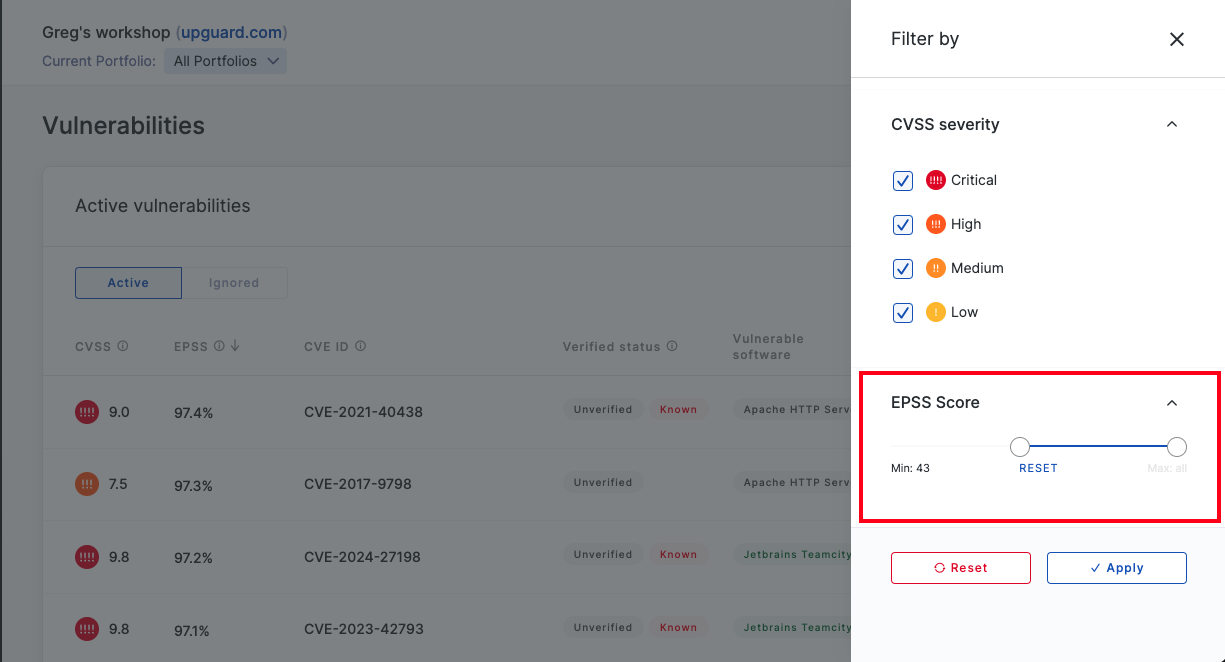
By selecting "Apply filters" you can also filter the list of Vulnerabilities by EPSS.