Watch Now

Vendor Risk in 3 Easy Steps
This beginner-level workshop introduces the fundamentals of third-party risk management using the platform to establish a scalable vendor monitoring process. It is ideal for new users looking to configure their environment and initiate their first evidence-based assessments.
What you’ll learn:
- Configuring vendor tiering systems and portfolios for structured organization.
- Onboarding vendors and leveraging security profiles for initial monitoring.
- Implementing an evidence-first approach using existing documentation to reduce questionnaire volume.
- Using AI-powered analysis to map vendor security postures against ISO 27001 and NIST frameworks.
- Generating customized risk assessments to communicate Breach Risk to stakeholders.
Duration: 51:35 minutes
Product Walk-through
This video provides a comprehensive introduction to the UpGuard platform, helping new users navigate the core modules for internal and external security monitoring. You will learn how to effectively manage your organization’s security posture and streamline third-party risk assessments.
What you’ll learn:
- A guided walkthrough of the dashboard and primary navigation tools.
- How to monitor your own attack surface and identify potential vulnerabilities.
- Techniques for evaluating third-party security ratings and automating risk assessments.
- Using Trust Pages to simplify security document sharing and build transparency.
- How to generate and customize reports for stakeholder communication.
Duration: 60 minutes

Product Walk-through: Breach Risk
This video explains how the platform identifies and monitors an organization's attack surface through automated scanning and security ratings. It is a vital resource for security teams looking to identify vulnerabilities, remediate risks, and benchmark their performance against competitors.
What you’ll learn:
- Evaluating security posture through automated scans and numeric risk ratings.
- Remediating or waiving discovered vulnerabilities to improve your score.
- Monitoring competitor risk profiles and benchmarking your Breach Risk.
- Generating historical reports to track security improvements over time.
- Managing breach notifications and identifying third-party vulnerabilities.
Duration: 21:37

Product Walk-through: Platform
This video provides a high-level overview of the platform's core features to help new users navigate their dashboard and manage vendor data. It is designed for administrators and analysts looking to streamline their daily workflow.
What you’ll learn:
- Navigating account activity and announcements on the home page.
- Tracking major updates through the My Tasks tab.
- Generating and scheduling customizable reports based on vendor assessments.
- Sharing reports via email and utilizing the support chat for inquiries.
- Monitoring overall Breach Risk and security trends.
Duration: 6:54 minutes

Product Walk-through: Settings
This video guides administrators through the account settings menu to customize platform functionality and manage internal user permissions. It helps team leads configure their environment to match specific organizational workflows and security requirements.
What you’ll learn:
- Managing user accounts, API keys, and group sharing permissions.
- Setting up co-branding for external emails and generated reports.
- Configuring custom notification alerts and default message fields.
- Organizing assets and portfolios using internal labels and tools.
- Utilizing control templates and document types within the content library to mitigate Breach Risk.
Duration: 5:20
Product Walk-through: Trust Exchange
This video demonstrates how to create and manage a Trust Page to automate vendor questionnaire responses and reduce manual workloads. It is a practical guide for security and compliance teams looking to scale their document sharing and improve efficiency.
What you’ll learn:
- Setting up a centralized Trust Page with custom branding and compliance badges.
- Building a content library to house frequently requested security documents.
- Tracking real-time access and downloads to monitor vendor engagement.
- Managing questionnaire tasks and configuring custom domains for your page.
- Implementing strategies to reduce Breach Risk through transparent documentation.
Duration: 4:31 minutes

Product Walk-through: Vendor Risk
This video outlines a structured approach to vendor risk management by utilizing tiering and AI-driven assessments to prioritize high-impact relationships. It helps risk managers and procurement teams efficiently evaluate vendor security postures and manage remediation.
What you’ll learn:
- Implementing vendor tiering to focus resources on the highest Breach Risk areas.
- Using AI to automate initial assessments and streamline information gathering.
- Deploying gap questionnaires to target specific security weaknesses.
- Managing remediation requests and tracking vendor ratings over time.
- Navigating the dashboard for a comprehensive view of organizational risk analysis.
Duration: 17:28 minutes

Adopt a Strategic Framework for Vendor Evaluations
This webinar introduces the Security Profile feature, offering a strategic framework to transition from traditional questionnaires to evidence-based vendor evaluations. It helps risk professionals automate document analysis and focus on high-impact security gaps.
What you’ll learn:
- Automating document analysis for SOC 2 reports and security policies.
- Leveraging automated scanning to instantly satisfy up to 26 security controls.
- Deploying targeted gap questionnaires to reduce vendor assessment fatigue.
- Mapping findings to ISO 27001 and NIST frameworks for compliance.
- Managing document classification and AI-generated assessments to lower Breach Risk.
Duration: 60 minutes

Workshop: Breach Risk
This workshop provides comprehensive training on managing your internal attack surface to improve and maintain a high security rating. It is designed for administrators and security teams who need to establish sustainable processes for internal risk management.
What you’ll learn:
- Confirming domains and organizing assets using portfolios and labels.
- Navigating the workflow to identify, remediate, or waive security risks.
- Configuring critical notifications for proactive monitoring of your attack surface.
- Utilizing advanced tools for typosquatting detection and identity breach management.
- Establishing competitor monitoring to benchmark your Breach Risk against peers.
Duration: 43:50
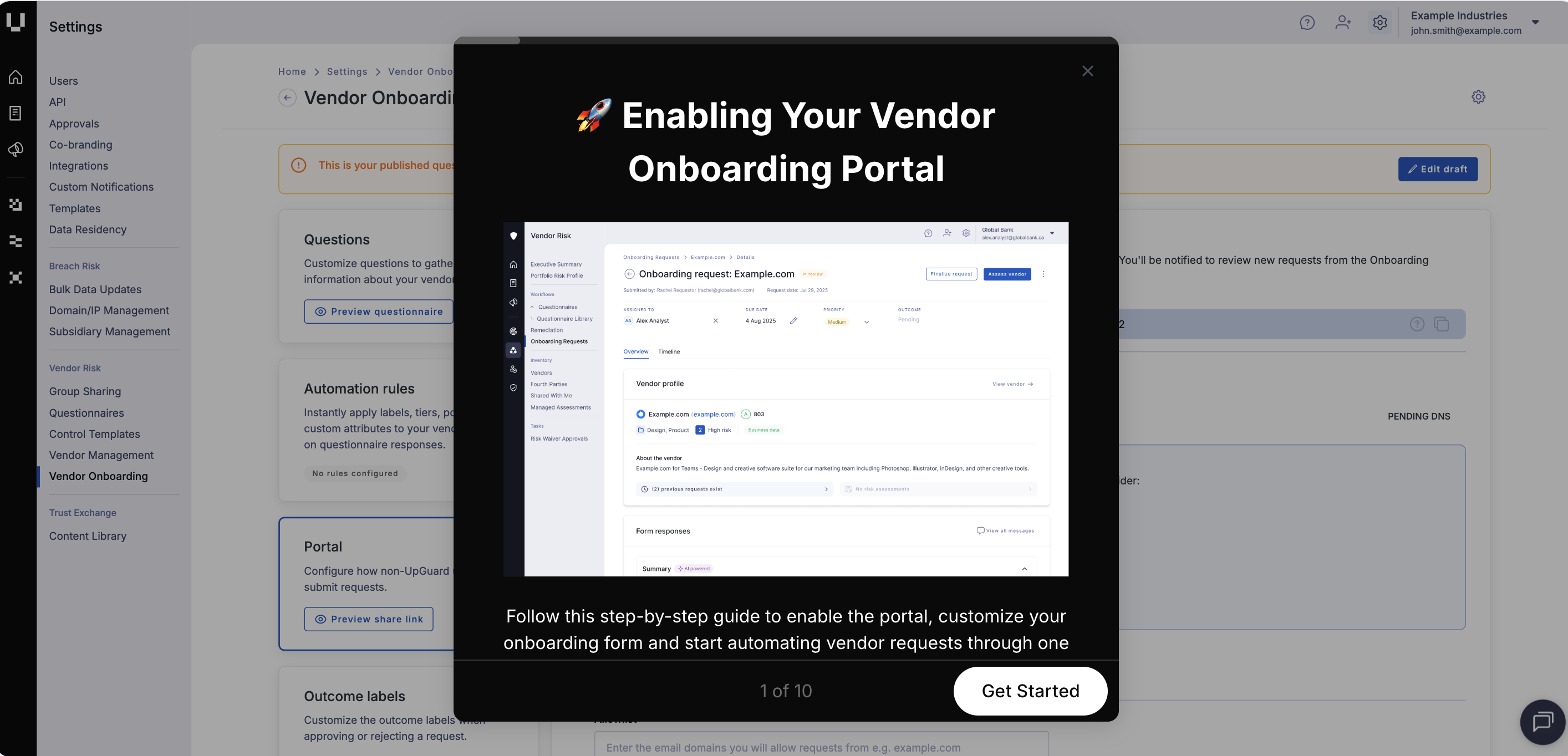
Vendor Onboarding Portal: Configuration Worklow
In this interactive product tour, we'll take you through the steps to confgiure the Vendor Onboarding Portal.
What you'll learn:
- How to enable the portal
- Customize your onboarding form
- Automate vendor requests through a secure, standardized intake workflow
Duration: 2 minutes